
Below is a compilation of security tips and best practices for being safe online and especially when interacting with Crypto/Blockchain dApps.
Read through each and take the assessment to test your knowledge.
Share with others so they can learn to be safe too!
Security Module Contents
- Passwords
- VPNs and Network
- 2 Factor Authentication
- Phishing and Social Engineering
- Keyloggers and Malware
- Software and Hardware Wallets
- Discord and Direct Messages
- Scams
- Malicious Smart Contracts
- Random NFT Airdrops
- Best Practices
Passwords

- Keep your passwords safe and secure.
- Make sure you are not reusing passwords across many sites.
- Utilize a password manager to generate and keep track of hard to remember passwords for more security.
VPNs/Network

- Avoid using public/shared networks if possible.
- If a public/shared network must be used, make sure you have a VPN set up to keep you safe.
- VPNs will encrypt your traffic and prevent others from intercepting your requests or seeing your data.
2 Factor Authentication
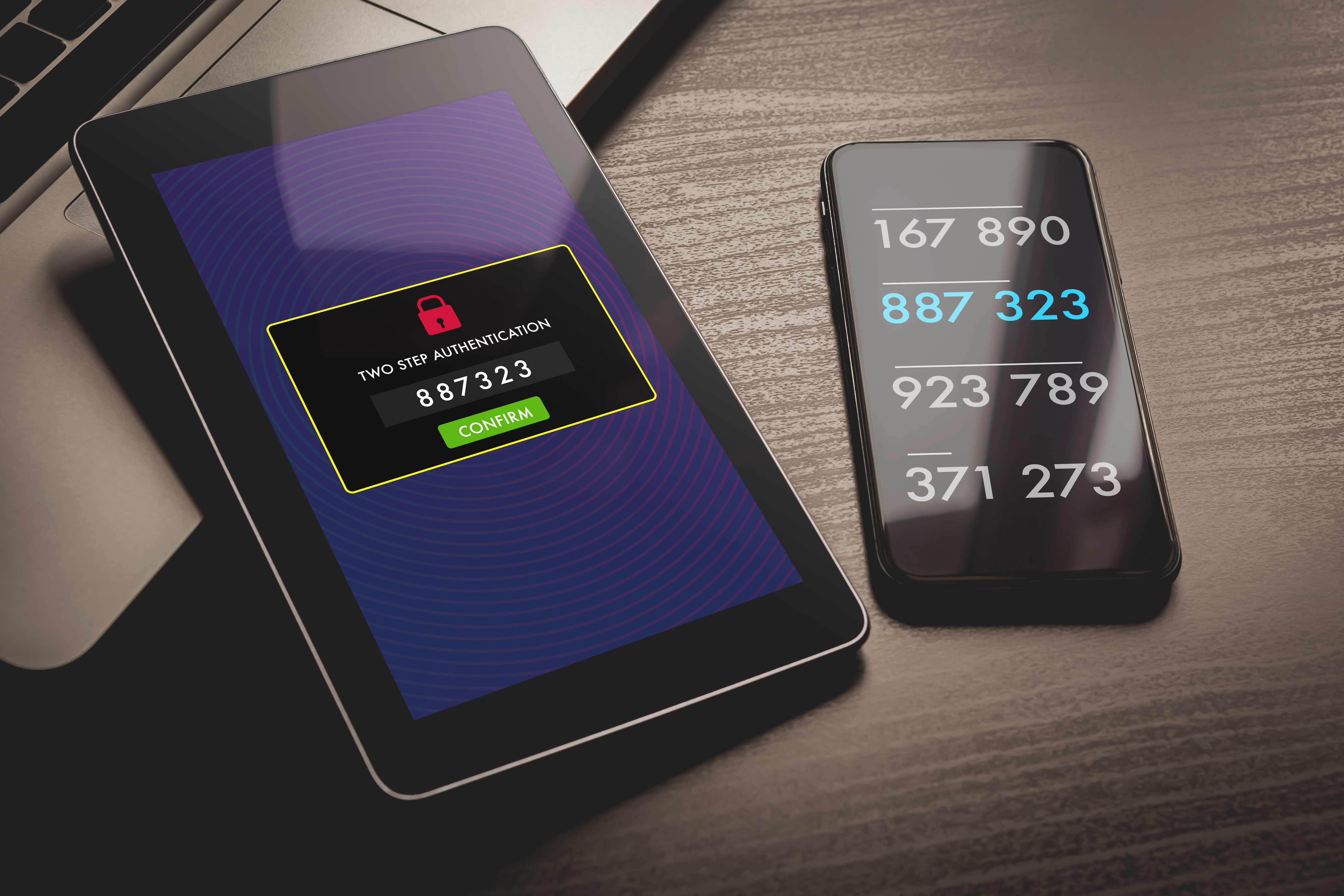
- Passwords get compromised all the time and networks are not always secure
- 2 Factor Authentication (2FA) adds an additional layer of security when accessing apps/services online
- When 2FA is enabled, you will need to approve requests using a pin/code/push from a third party application
- Having 2 layers of security helps prevent your accounts and assets from being compromised if your credentials are exposed
Phishing and Social Engineering

- Social Engineering is the practice of using someone’s natural behaviors and tendencies against them
- Social Engineering is often employed to get the target individual to reveal/disclose sensitive information they otherwise would not share
- Phishing uses Social Engineering techniques to get a target to provide access to account credentials
- Phishing attacks can be very sophisticated and clever in their design requiring you to be aware of these risks and to be on the lookout for suspicious clues and red flags
Keyloggers and Malware

- Software designed for a malicous purpose is referred to as Malware
- Malware comes in many forms and may infect your devices in different ways
- Keyloggers are a type of malware that monitor your typing and record keystrokes being sent to your keyboard
- This data can be sent to other servers to people looking to abuse this info (credit cards, passwords, contacts, recovery seeds)
Software and Hardware Wallets

- Software wallets such as Metamask and Coinbase Wallet exist as programs/browser extensions on your devices and often are partly custodied with a third party
- Hardware wallets like Ledger and Trezor run on physical devices with your private keys stored on the device instead of your connected devices or online
- Connecting a hardware wallet to a software wallet like Metamask allows the hardware wallet to be used as a 2FA device requiring you to approve transactions both in the software and on the physical device
- Using the combination of a Software and Hardware wallet allows you to conveniently access your favorite dApps without compromising on security
- NEVER Ever disclose your Secret Recovery or Seed Phrase to ANYONE as this will enable the holder to fully access and control your wallet
Discord and Direct Messages

- Discord is one of the most popular platforms for Blockchain, Crypto, and NFTs.
- Many Discord integrations prompt you to connect metamask or enter some other potentially sensitive information.
- It’s important to be cautious when using this platform and clicking links or interacting with bots.
- Direct Messages containing spammy and potentially malicious links are common and must be treated appropriately.
- Always verify Direct Messages you receive are truly from the person you think and not someone posing as a trusted individual.
Scams

- As with any potentially profitable field, there are many scammers in the Crypto, Blockchain, and NFT space.
- If an offer sounds too good to be true, it generally is too good to be true and should be approached with extreme skepticism.
- Always check with other trusted communities when presented with something that seems like a scam.
- Scams are only effective when the targets don’t know what to be on the lookout for.
- Share instances of potential scams with others to keep everyone aware and safe.
Malicious Smart Contracts

- Just like traditional software applications, a dApp may also contain vulnerabilities.
- These may sometimes be accidentally introduced through inexperienced or careless developers or intentially by more malicious parties.
- A malicious smart contract may attempt to trick you into paying an exorbitant amount of crypto to the contract/address or transfer your other assets/NFTs against your will.
- Enabling 2 Factor and using a Hardware Wallet are critical steps to prevent being vulnerable to these exploits.
- Use empty wallets for minting new projects to reduce the potential impact in case you do get compromised.
- Always be safe and vigilant and share info with others when unsure as to how safe a particular action may be.
Random NFT Airdrops

- After some time in the NFT space you will from time to time notice a random NFT in your account that you do not recognize.
- These airdropped NFTs tend to be scams and are involved in a variety of attacks.
- A dusting attack will track wallets that attempt to spend or sell these assets which allows the trackers to deanonymize wallet addresses and better social engineer them.
- Potentially malicious smart contracts may also be connected to these NFTs that will prompt you to transfer crypto and other assets out of your wallet when attempting to sell or transfer the airdropped NFT.
- Best practice for these airdropped NFTs is to hide the NFT from your account so that you do not accidentally interact with it.
- Hiding the NFT will not get rid of it from your account but it will prevent a malicious interaction from taking place in your wallet that could have major consequences.
Best Practices

- Security is a team effort requiring us all to be diligent about identifying, addressing, and informing others as to potential security risks
- Never click links you don’t recognize and always double check links you do recognize to ensure the destination address is fully correct
- Always verify the person messaging you in your DMs is the person you think it is and not an impostor pretending to be someone else
- Keep your device software up to date to prevent security vulnerabilities from being exploited
- Never leave your device unattended to avoid physical compromise of your systems
Share With Others
Find the Security Module helpful? Share with others so they can be safe too! Together we win!